By Joshua Vienneau, Senior Product Manager
This article explains how integrators and administrators can leverage Brightspace Service Users and OAuth 2.0 client credentials to authenticate secure server-to-server integrations, automate workflows, and manage machine-to-machine API access without human accounts.
Introduction
Across the Brightspace ecosystem, developers and administrators have been asking for a simpler, more secure way to support integrations, automations, and background services, without relying on human accounts or long-lived tokens. Today, we are excited to announce a major step forward in meeting that need: Service Users, a new type of non-human identity designed specifically for machine-to-machine (M2M) workloads.
Service Users, combined with Brightspace’s new OAuth 2.0 Client Credentials Grant with JWT Client Assertions, provide a modern, standards-based, least-privilege authentication model for automated integrations. Together, they enable secure access to APIs without user prompts, browser redirects, or refresh tokens.
This major improvement to Brightspace opens the door to cleaner, safer, and more maintainable integrations across the platform.
What are Service Users?
Service Users are specialized Brightspace user accounts designed for automated systems and integrations. Unlike standard human accounts, they:
- Have non-interactive API authentication
- Follow strict least-privilege principles
- Are linked to a single application
- Support tightly scoped permissions using Brightspace roles
- Participate in the organization access model in predictable ways
You can think of them as machine operators in your Brightspace environment. These accounts act on behalf of an application rather than a person and have only the permissions that administrators choose to grant.
Why we built Service Users
Institutions and partners have consistently requested a first-class solution for:
- Scheduled SIS or middleware sync jobs
- Automated background processes
- Server-side analytics generation
- Content refresh and catalog sync operations
- System-to-system bridges across institutional infrastructure
These scenarios were difficult to support using delegated OAuth flows designed for human users. Service Users provide a proper identity model for automated access that is transparent, secure and aligned with the needs of non-interactive workloads.
How Service Users Fit into Brightspace Security
The Service Users tool builds directly on the Brightspace user-role model and follows the same core authorization principles that administrators already know.
Cascading access
Service users can be enrolled at any level in the Brightspace organization structure. These enrollments can cascade down through org units when appropriate. This allows an integration to access exactly the courses or org units it needs, without granting unnecessary access. Administrators can manage these enrollments and permissions using the same models they already use for human accounts.
Clear UI separation
To keep administration clean and to avoid mixing automated identities with real people:
- Service Users appear in a dedicated location under Manage Extensibility.
- They are excluded from standard classlists, user searches, exports, data sets, and non-relevant APIs.
- Configuration options are streamlined to focus on integration and access control.
This separation ensures that automated service identities remain easy to manage and clearly distinct from human users.
Introducing OAuth 2.0 client credentials with JWT client assertions
To support Service Users, Brightspace now provides a robust new authentication flow based on OAuth 2.0.
Client Credentials Grant (CCG)
The Client Credentials Grant is designed for machine-to-machine authentication, where an application authenticates as itself.
JWT client assertions
Unlike traditional client secrets, a client assertion is a short-lived, signed JSON Web Token created using the application’s private key. Brightspace validates it using the public keys stored in a JWKS that the administrator specifies during application registration.
This approach provides:
- No shared secrets to manage
- Protection against replay attacks
- Short-lived, non-refreshable tokens
- Strong asymmetric cryptography
- Alignment with OAuth 2.0 best practices (RFC 7523, RFC 7519, RFC 6749)
It strikes a balance between flexibility for developers and strong security for administrators.
How Service Users work with client credentials
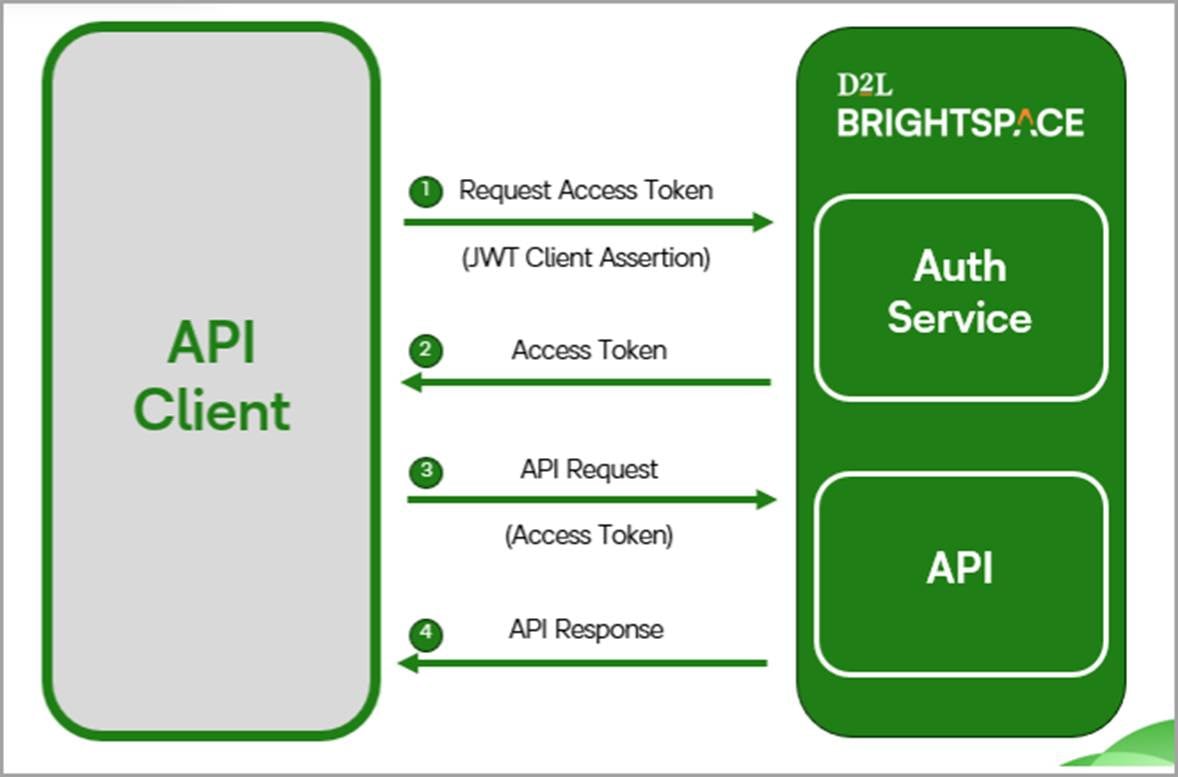
Each OAuth2.0 client-credentials application must be associated with a service user. When the application requests a token:
- It sends a signed JWT assertion.
- Brightspace validates the signature using the registered JWKS.
- Brightspace issues a short-lived access token.
- Any API call made using that token is performed with the permissions of the associated service user.
This pairing ensures predictable least-privilege access and simple integration lifecycle management. If an integration needs to be disabled, administrators can revoke access instantly by disabling the service user or updating the application’s keys.
Registering an application: a quick look
To register a client-credentials application in Brightspace, administrators simply:
- Create a service user
- Assign narrowly scoped permissions
- Register an OAuth application and specify the JWKS URL
- Link the service user to the application
- Test and deploy
This workflow keeps configuration lightweight and helps institutions maintain strong security boundaries.

Figure: New options for registering an OAuth 2.0 application in Brightspace.
When to use each OAuth flow
Scenario | Recommended Flow |
|---|
A human logs in and grants access | Authorization Code plus Refresh Tokens |
A backend system needs ongoing access with no user present | Client Credentials plus Service User |
Scheduled tasks, data pipelines, middleware, background syncs | Client Credentials plus Service User |
Note: If there is no human involved, the application should authenticate as itself using a service user.
What this means for developers and administrators
With Service Users and the new OAuth2.0 Client Credentials Grant, Brightspace now offers:
- A modern authentication approach built on industry standards
- Strong security without shared secrets
- Clear separation between human and machine accounts
- Fine-grained API permission control
- Straightforward integration lifecycle management
- A scalable foundation for future extensibility improvements
These capabilities strengthen the overall Brightspace integration experience for institutions and developers.
What comes next
We will continue to expand the documentation, examples, and developer tooling that support OAuth and Brightspace integrations. This release provides important groundwork for future improvements in how administrators configure and manage integrations.
If you are building or maintaining integrations with Brightspace, keep an eye on upcoming release notes and updates to our developer documentation.
Additional Resources